Operating on a stable, reliable, and secure network is very important for many businesses. Because of that, VPNs have become an important asset that helps companies and employees connect to the applications, data, tools, and resources they need without risking exposing or compromising their data.
A VPN (Virtual Private Network) allows users to safely connect to another network over the Internet by encrypting the connection from their phone, computer, and other devices. A VPN makes your Internet connection more secure and offers both privacy and anonymity online.
This is why organizations often rely upon the security provided by VPNs to protect their data against interception, hence the idea of business VPN. A B2B VPN works in the exact same way as a personal VPN, but it serves a different, more important purpose. In essence, a business VPN helps employees, especially those working remotely, access internal applications and data, or create a single shared network between multiple office locations.
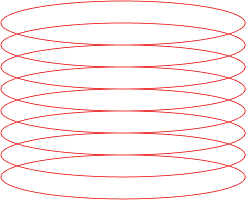
A business VPN provides a tunnel between your organization’s resources and the employees accessing them. Because the respective tunnel is encrypted end-to-end, companies do not have to worry about unwanted network visibility or access. And that’s the key role a business VPN plays.
Why are business VPNs so important for companies?
As we mentioned before, such solutions are considered important for maintaining a secure and private network connection between employees and the company’s data. And since working from home is still widely-practiced, business VPNs facilitate remote access to precious data that needs to be accessed and stored within the organization only.
But why is a business VPN so important for accomplishing this? Well, it’s all about how you access the data, ergo the Internet. A business VPN allows remote working employees to connect to a business’s local network securely, instead of connecting directly via the public Internet.
Those users can then access corporate services and software as if they were on-site without worrying about exposing potentially sensitive corporate information. This is highly beneficial, especially for smaller businesses that have limited resources to devote to managing security.
A lot of companies integrate B2B VPNs thanks to their versatility. Higher bit encryption consolidates security while server locations can enhance your security by trusting VPN servers in reputable countries. Most business VPNs also incorporate an anonymous DNS server and offer router support. If you are planning to use a business VPN, you can check here a list of some of the most popular business VPNs, courtesy of Comparitech.
What are the two categories of business VPNs?
Business VPNs can be classified into two categories: remote access VPNs, and site-to-site VPNs. Let’s discuss each of them and see how they work.
Remote Access VPNs establish a connection between individual users and a remote network, in this case, the business’ internal network. This type of VPNs uses two important components:
- Network Access Server (NAS): a dedicated server, or a software application on a shared server, which is connected to the business’s internal network;
- VPN client, which is software installed on a user’s device.
When using a remote access VPN, all the data users send and receive from the network infrastructure is encrypted. They do this by activating their VPN client, which, in turn, establishes an encrypted ‘tunnel’ to the NAS.
Thus, everything that is stored in the corporate data center and headquarters is protected and can be safely accessed, irrespective of the public connection to the Internet. Business VPNs discourage intercepting or tampering with data thanks to the powerful remote access encryption.
Site-to-site VPNs create a single virtual network that can be shared across multiple offices in different geographic locations that need ongoing access to the corporate network. In this case, the VPN client is hosted on the local network of each office, rather than on individual users’ devices. The result is that users in each office location are able to access the shared network without using a VPN client individually. With a site-to-site VPN, a company can securely connect its corporate network with its remote offices to communicate and share resources with them as a single network.
What are the most recurrent limitations of business VPNs?
VPNs are cheaper and easier to manage than legacy solutions. Despite their popularity, both business VPN connection types (remote access VPN and site-to-site VPN) have some limitations you should be aware of, particularly when it comes to ensuring thorough protection.
First, it is important to understand that even business VPNs are susceptible to security breaches. A remote employee’s VPN credentials might be compromised, thus allowing the attacker to gain access to all applications and data on that network.
In addition, despite the ever growing use of cloud-based apps, many organizations find cloud-based business VPNs neither well-optimized nor that secure. If a company uses a cloud-based VPN, its Network Access Server operates in a data center in a different physical location from the company’s internal network. This is a counterintuitive extra step that adds latency to every single request between employees and the network, slowing down performance and stability.
This brings us to the idea of inconsistency and incompatibility. Depending on the business practice, its applications can be hosted in the cloud rather than on the internal network. These formats are often incompatible with VPNs, and, on top of that, many of these cloud-based apps have their own security tools. In the end, users cannot fully control or understand these security implementations and might fail to adapt them to meet the needs of their business.
There is also the hardware that needs to be properly taken into consideration if you are using, for example, a Network Attached System in order to connect with the employees’ VPN clients. This process requires the company to regularly upgrade its hardware assets to make sure they offer comprehensive protection against cyber attacks. The same concerns go for users who exceed the Network Access Server’s traffic limit, which in turn brings the risk of overloading and crashing.
Finally, managing business VPNs can take a lot of time. Being able to configure them the proper way can be very daunting, especially if a business uses more than one VPN to provide different varieties of access to different types of employees. You could think about installing the right VPN client on every remote employee’s computer, and then making sure employees are keeping that software up-to-date.
What are the main differences between business VPNs and commercial VPNs?
While both of them work similarly in establishing an encrypted connection with a remote network, the difference lies in the way in which they are used. Commercial VPNs are usually used for individual preferences like unblocking a website or service while maintaining privacy and anonymity, while business VPNs are used for business security and data protection.
Business VPNs offer a dedicated IP address with a dedicated server, all of these specifically designed for corporate needs. By contrast, the IP for the commercial VPNs might be shared with other users and can change every time you connect to the service.
Additionally, it’s highly likely that a business VPN is designed for multiple users. More specifically, the employees use one universal account that is fully controlled by an account manager. Therefore, the account manager has access to all the websites the employees are visiting while the VPN is active.
Conclusion
In a B2B environment, business VPNs are a cheap and versatile solution that helps companies consolidate the security of their networks. Such tools are important for countless businesses and provide a safe means for remote-working employees to access the corporate network via a public Internet connection.
However, organizations need to look beyond VPN capabilities to ensure devices connecting to the corporate network remain secure and do not compromise the data that’s moving between the device and the network. For those interested, we also explain the differences between a VPN and a proxy in our dedicated article.