Online security and privacy are two of the most important aspects of both corporate and commercial environments. Just as you use solutions like VPNs to ensure anonymity and extended access across the Internet, so do companies. Many businesses rely upon a VPN and/or a proxy to keep their data secure when accessed remotely. It’s interesting to note that, theoretically, VPNs and proxies are quite similar. While this is true to some extent, there are also some important distinctions between these two solutions.
A VPN (Virtual Private Network) is a tool that allows users to safely and anonymously connect to another network over the Internet by encrypting the connection from their phone, computer, and other devices. The main advantage of a VPN is the ability to surf across the World Wide Web without having to worry about privacy or security issues. This is why business VPNs have become an important asset for many companies around the world, as you can read in our previous article.
A proxy is a server that acts as a gateway, and intermediary between your device and the website you are visiting. Proxy servers offer varying levels of functionality, security, and privacy depending on your use case, needs, or company policy. Proxy servers act as a firewall and web filter and have several benefits, such as cache data to accelerate the speed of common requests, privacy and security by protecting the user from the risks lurking across the Internet, but it does so by hiding only the device IP address.
How does a VPN function?
To provide the users with privacy and security, VPNs make use of end-to-end encryption. It routes your data through an encrypted tunnel, so no one can see your web activity or expose your data, mainly because the encryption makes it impossible to decipher. This encryption is often referred to as VPN Tunnel.
Tunneling hides and tunnels your data from the rest of the Internet. However, perks do not stop here. Tunneling also ensures that your location will remain unknown, except for you and the server that you are connected to. So, instead of your IP address, the tunnel sends out the IP address of the host server that the VPN is running through.
The inner workings of a VPN are based on complex protocols. For example, there are several types of encryption, such as hashing, symmetric cryptography, and asymmetric cryptography. Similarly, tunneling has a couple of different protocols as well. These include Point-to-Point Tunneling Protocol (PPTP), Layer 2 Tunnel Protocol (L2TP), Open VPN, and Secure Socket Tunneling Protocol (SSTP).
How does a proxy server work?
Every device must have an IP address to communicate with the Internet. To put it simply, a proxy server is a gateway with its IP address that your computer knows. Whenever you send a web request, it goes to the proxy server first. Then, the proxy makes your web request on your behalf, collects the response from the web server, and forwards you the web page data. This is the process that helps display the web page into your browser for you to visit.
When the proxy server forwards your web requests, it can make changes to the data you send while keeping the information you expect to see. Furthermore, a proxy server can change your IP address, so the web server is not able to retrieve your location. A proxy server can also encrypt your data to be unreadable in transit. And lastly, a proxy server can block access to certain web pages, based on IP address.
The main types of proxy servers
Although they are quite similar in purpose, not all proxy servers work in the same way. Such is the case with different types of VPNs. Because of that, it is important to make sure the proxy server you opt for meets your use case
- HTTP proxies – These are used only for web pages, most commonly for accessing geo-restricted websites. In short, all your browser traffic is rerouted through this proxy server.
- Transparent proxies – They serve the opposite purpose of HTTP proxies while giving your IP address to the website you are visiting. Instead of granting access to restricted websites, they can be easily set up to block the users’ access to certain pages and monitor their online activity. Businesses, public libraries, and schools often use transparent proxies for content filtering and site restriction.
- Anonymous proxies – They do not give your IP address to the website you are visiting. Anonymous proxies are primarily used to avoid identity theft and maintain online privacy. They can also prevent a website from showing you targeted marketing content based on your location. In addition, they can help you get around blocked content or restricted content
- SOCKS5 proxies – They are not limited to web traffic, hence their popularity. SOCKS5 proxies are great for file sharing and streaming because they break the data they send into smaller packages. Therefore, it offers faster download speeds that outmatch a VPN.
- Distorting proxies – A distorting proxy server shows a false IP address while identifying itself as a proxy. Distorting proxies are similar to anonymous proxies, but distorting proxies can also help you access geo-restricted sites, since they are passing along a false IP address.
- High Anonymity proxies, sometimes Elite Level 1 Proxies – They offer the most private and secure way to read the Internet, because they periodically change the IP address they present to the web server, making it very hard to read and keep track of online traffic. One of the most popular examples is Tor.
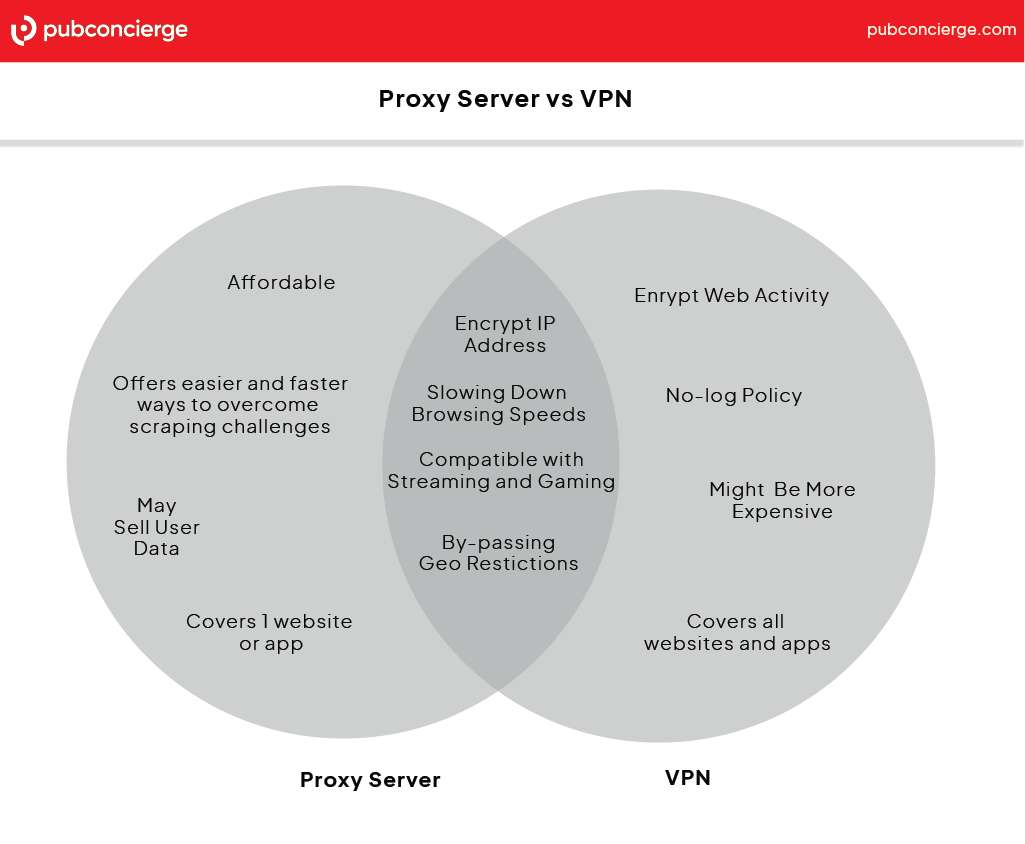
What are the similarities between proxies and VPNs?
By definition, a proxy server and a VPN are pretty much similar. They both help with privacy and give your company a safe and reliable way of remotely accessing your corporate network. Here are the key similarities between a proxy server and a VPN:
- They both hide your IP address – Proxy servers and VPNs do a great job in concealing your IP address since entities are not able to read your actual address, but rather the IP address of the proxy or VPN.
- They both help bypass geo-restrictions – Proxies and VPNs mask your IP address ito give you access to content that might otherwise be unavailable in your country or region. However, VPNs are more reliable in bypassing such restrictions.
- They both suffer from (relatively) slow speed – Both methods impact your browsing speed to a certain extent. In VPNs, slow speeds are due to the encryption overhead. Proxies are generally considered to be slower because they act as a middleman between your device and the website you are accessing.
What are the differences between proxies and VPNs?
Although their purpose and qualities often overlap, proxies and VPNs feature important differences. It is important to eliminate confusion and have a clear understanding of what does what to choose the right option for your use case.
VPNs encrypt your entire internet connection. The main difference between a proxy and a VPN is encryption. The latter makes use of solid encryption protocols to hide not only your IP address but also your entire online activity. No one will be able to track and decrypt your data if you are using a VPN. By contrast, a proxy server will only hide your IP address without encrypting your activity on the web.
Traffic rerouting is not ensured in its entirety by proxy servers. That’s because VPNs tunnel your internet connection on the operating system level, thus rerouting all your traffic. Any incoming or outgoing connections have to pass through the VPN. On the other hand, proxy servers work on the application level. They route web traffic or traffic only from certain apps that allow proxy connections.
Many popular VPNs have a strict no-log policy. They do not store or log your online activity when using them. As a result, your data remains private at all times. Unlike VPNs, many proxy servers keep connection logs and in some cases even activity logs.
VPNs offer a more reliable connection than proxies. Generally speaking, proxy connections drop more frequently. On the other hand, VPNs are more stable and reliable while likely offering useful features such as killswitches and/or leak protections. These features ensure your privacy and security are not compromised, should the VPN connection drop. In addition, VPNs are more efficient in avoiding or mitigating server congestion.
Proxy scraping is a faster and easier way to collect data rather than scraping via VPN. Data collection can be a magnet for obstacles, especially if you plan on gathering huge amounts of data from many different websites. Some of the most common challenges include CAPTCHAs, IP blocking, and slow website speeds. Scraping with proxies is one of the best methods to overcome these challenges and streamline the process of collecting data while still maintaining online safety. Proxies decrease the risk of your crawler or spider getting blocked by websites.
Typically, companies use two types of proxies for this purpose: reverse proxy and forward proxy. Both of these proxies can be used to ease access to a server. They are also used for decryption, caching, authentication, and load-balancing, leading to faster load times and easier access to the target site’s data. VPNs are not so advantageous because they are not designed to handle large quantities of web scraping activity. In addition, because of the encryption process, the traffic is slower.
Proxy server or VPN? What should you choose?
Depending on your needs, you might want to either use a VPN or a proxy. In corporate environments, VPNs are a popular choice, but this doesn’t necessarily mean businesses cannot use proxy servers for specific situations.
Therefore, you should use a VPN service if:
- You need coverage of all websites and applications. VPNs work on the operating system level, therefore they reroute all the incoming and outgoing traffic. VPNs are more versatile in covering more than just a specific website or app.
- You need to encrypt your data as well. Proxy servers only mask your IP address. By contrast, a VPN service not only hides your IP from hackers or ISPs, but also encrypts your online activity and protects your data entirely.
- You need more functionalities. Many VPNs have built-in features that allow you to customize their use and protect against data breaches if the connection suddenly drops.
- By extension, if you need more reliability and speed. Proxy servers are slower than VPNs in terms of connection speeds. They tend to drop more often and have a higher chance of congestion/getting overloaded.
You should use a proxy server if:
- You want to collect data faster, safer, and easier. This is one of the most popular and important use cases for a proxy server. As we said before, proxy scraping is a successful and efficient way to collect large volumes of data from websites. It allows for greater versatility, even for those who use the cURL command line to collect data. The right configuration allows you to efficiently curl with proxy and gather the information you need.
- You only need one website or app’s IP address hidden. If you need a one-and-one, getting a proxy server to cover a single website or app is quicker, cheaper, and more efficient.
- You want a quick way of restricting online activity. Companies, schools, and libraries often use proxy servers for content filtering. It allows for online activity monitoring and gives access only to specific websites.
Recap
While it’s true proxies and VPNs tend to serve the same purpose, in the end, it all comes down to the company’s needs. VPNs and Proxy servers are great tools for things like bypassing restrictions, hiding your IP address, and giving you privacy. However, each method is best suited for specific needs.