Have you ever received unsolicited emails, been locked out of your social media account, or experienced a sudden drop in Internet speed? These are all possible signs of IP address abuse.
The dark side of technological advancement, IP abuse, is a serious issue that needs to be understood if we want to keep our resources and devices safe from harm.
Whether it’s a small spammy email or a suspicious site that somehow tricked you into typing your credentials, IP abuse can take many forms. The worst part is, even through small online scams, IP abuse can seriously damage a company’s network and connected devices.
So, can you actually spot the early signs of IP abuse? What are the most common ways a hacker can abuse your IP? Can you do something about that and keep a malicious IP address out of your business? Read on to find out.
What is IP abuse?
IPs are unique identifiers assigned to every single online device. The devices use IPs to communicate with each other over the Internet. IPs are used to route data between different networks and devices because they act as a street address where the postman delivers a package.
While it seems nice and easy at first, things can go south relatively often. IP abuse can happen anytime, and for that, it’s important to understand how it can happen before learning how to prevent it or quickly fix the issues.
IP abuse refers to any activity that misuses or exploits the IP address of a device to engage in harmful or illegal actions. IP abuse can take many forms, including spamming, phishing, hacking, and denial-of-service (DoS) attacks.
These activities can be carried out by individuals, groups, or organizations for various purposes, such as stealing personal information, spreading malware, or disrupting online services.
Examples of IP abuse include sending large amounts of spam emails or messages, using malware to take control of a device, or flooding a website with traffic to overwhelm its servers and cause it to crash.
IP abuse is a serious issue that can harm individuals and businesses. It can result in financial losses, reputational damage, and legal consequences for those involved.
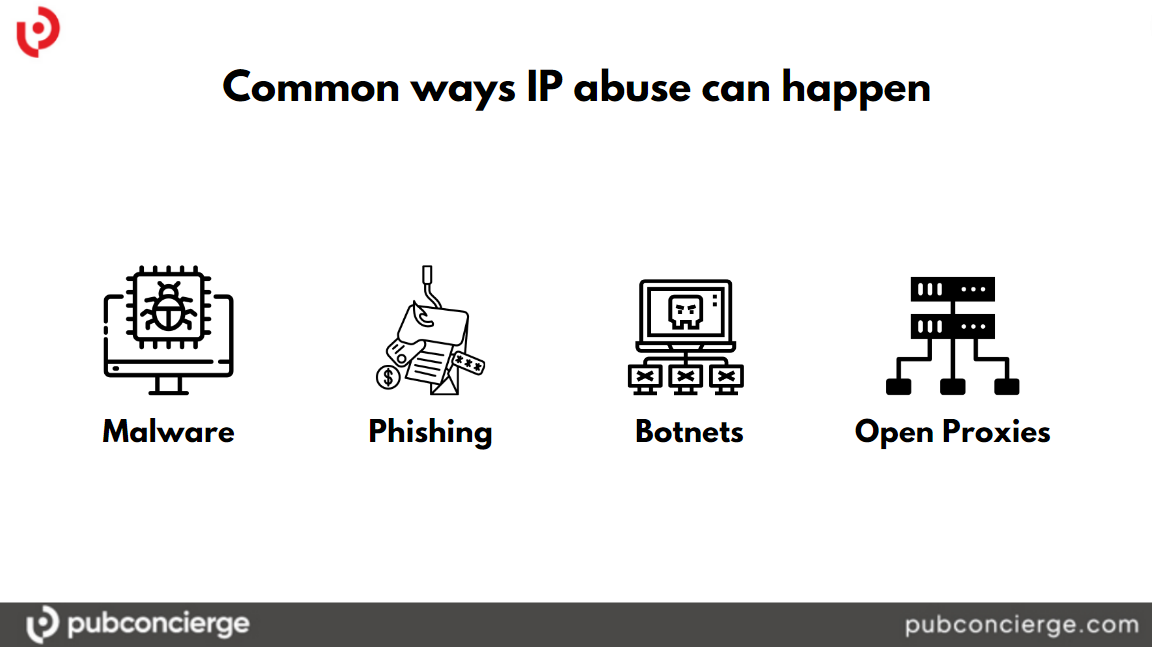
How can IP abuse happen?
The online world evolved rapidly, as did cyber attacks and any such illicit activities. IP abuse can happen in many ways, and it often involves exploiting vulnerabilities in networks, software, or devices. Remember what we discussed about IP hijacking? Well, things need to be taken seriously.
Let’s see the most prominent ways IP abuse can occur.
Malware
Malware, such as viruses, trojans, and spyware, can be used to gain unauthorized access to a device and take control of its IP address. Once an attacker gains control of an IP address, they can use it to launch attacks on other devices or networks, spread malware, or engage in other malicious activities.
Phishing
Phishing is a type of social engineering attack where hijackers use fraudulent emails, messages, or websites to trick people into revealing their personal information or login credentials. By gaining access to someone’s login credentials, attackers can use their IP address to access their accounts and engage in malicious activities, such as sending spam or stealing data.
Botnets
Botnets are networks of compromised devices that can be used to carry out coordinated attacks on other devices or networks. By infecting devices with malware and taking control of their IP addresses, attackers can use botnets to launch denial-of-service attacks, spam campaigns, or other forms of cybercrime.
Open proxies
Open proxies are public servers that can be used to access the Internet anonymously. While open proxies can be useful for privacy, they can also be used to engage in malicious activities, such as sending spam or launching attacks on other networks. Attackers can use these proxies to hide their IP addresses and make it more difficult for authorities to track their activities.
How can you detect IP abuse?
Detecting IP abuse can be challenging, as it often involves malicious actors who take steps to hide their activities and evade detection. However, there are signs that you can look for that may indicate that IP abuse is occurring. Here are a few common ways to detect IP abuse:
Unusual network activity
If you notice unusual network activity, such as slow performance or dropped connections, it may be a sign that your device or network is being targeted by an attacker.
Suspicious logins
If you see login attempts on your accounts from unfamiliar IP addresses or locations, it may be a sign that your login credentials have been compromised.
Unsolicited emails or messages
If you receive large amounts of unsolicited emails or messages, especially those that contain suspicious links or attachments, your email address or device might have been targeted by spammers or phishers.
Unusual system behavior
Instances like programs crashing or files disappearing may be another sign your system has been corrupted and malware is spreading.
Unexplained charges or transactions
If you notice unexplained charges or transactions on your credit card or bank account, it may be a sign that your personal information has been stolen and is being used fraudulently.
Tools you can use to detect IP abuse incidents
There are several tools available that can be used for detecting IP abuse. Here are some examples:
Network monitoring tools
These tools allow you to monitor your network traffic for unusual or suspicious activity. Network monitoring tools can help you detect potential attacks, such as Distributed Denial of Service (DDoS) attacks or unauthorized access attempts.
Here are a few examples of such software.
PRTG Network Monitor: PRTG is a comprehensive network monitoring tool that provides real-time network performance data and alerts. It offers a range of features, including bandwidth monitoring, network mapping, and customizable dashboards.
SolarWinds Network Performance Monitor: SolarWinds is a popular network monitoring tool that provides real-time performance data and alerts. It offers features such as network topology mapping, custom dashboards, and automated network discovery.
Nagios: Nagios is an open-source network monitoring tool that provides real-time monitoring of hosts, services, and network devices. It offers features such as network mapping, event handling, and alerting.
Zabbix: Zabbix is another open-source network monitoring tool that provides real-time monitoring of hosts, services, and network devices. It offers features such as network mapping, trend analysis, and customizable alerts.
Wireshark: Wireshark is a popular network protocol analyzer that allows you to capture and analyze network traffic. It can help you diagnose network problems, troubleshoot security issues, and optimize network performance.
Firewalls
Firewalls are security devices that monitor and filter incoming and outgoing network traffic based on a set of predefined rules. Firewalls can help you detect and block traffic that is associated with IP abuse.
Intrusion detection systems (IDS)
IDS tools are designed to detect and alert you to potential attacks on your network. IDS tools can detect a wide range of IP abuse, including network scanning, port scanning, and malware infections.
Snort: Snort is a free and open-source IDS tool that can be used for network intrusion detection and prevention. It can detect a wide range of network-based attacks, including buffer overflow attacks, stealth port scans, and CGI attacks.
Suricata: Suricata is another free and open-source IDS tool that can be used for network intrusion detection and prevention. It is designed to be high-performance and can handle a large volume of traffic. It can detect a wide range of network-based attacks, including malware and command-and-control traffic.
Zeek (formerly known as Bro): This is a free and open-source network analysis framework that can be used for network intrusion detection and prevention. It provides powerful network analysis functions and can detect a wide range of network-based attacks.
OSSEC: OSSEC is an open-source IDS tool that can be used for host-based intrusion detection and prevention. It can detect a wide range of attacks, including rootkits, file changes, and unauthorized access.
How to report IP abuse?
If you suspect that you have been the victim of IP abuse, or if you have witnessed IP abuse occurring, it is important to report it to the appropriate authorities. Here are some steps you can take to report IP abuse:
Contact your Internet Service Provider (ISP)
Your ISP is often the first point of contact for reporting IP abuse. They can help you identify the source of the abuse and take steps to stop it. Your ISP may also have tools or resources to help you prevent future IP abuse.
Report to law enforcement agencies
If you believe that IP abuse involves criminal activity, such as hacking or phishing, you should report it to the relevant law enforcement agencies. You can contact your local police department or the Federal Bureau of Investigation (FBI) if the activity crosses state or national borders.
Report to the website or service provider
If IP abuse is occurring on a website or online service, you can report it to the website or service provider. Most websites and services have a way to report abusive activity, such as a “Report Abuse” button or a contact email address.
Contact a cybersecurity expert
If you are unsure how to report IP abuse or need assistance in investigating the activity, you may want to reach out to a cybersecurity expert. They can help you identify the source of the abuse and take steps to protect your devices and data.
Use IP abuse reporting tools
There are different tools available that can help you report IP abuse, such as antivirus software, IP blacklists, abuse reporting forms, and databases. These tools can help you identify the source of the abuse and report it to the appropriate authorities.
Antivirus software
Antivirus software is designed to detect and remove malware, such as viruses, trojans, and spyware, from your computer. Antivirus software can help you detect IP abuse that is related to malware infections.
IP blacklist tools
IP blacklist tools can be used to identify IP addresses that have been associated with malicious activity, such as spamming, phishing, and malware distribution. IP blacklist tools can help you block traffic from known malicious IP addresses.
These tools can be used in combination to help detect and prevent IP abuse. It is important to regularly update and maintain these tools to ensure they are effective in detecting and blocking potential threats. Here are a couple of popular IP blacklisting tools you can use to check a specific address.
Spamhaus: You can enter your IP address in the search bar and do a quick, yet effective lookup. The resulting message should tell you whether your IP address has no issues or if it’s been found on the Spamhaus blacklist database. In that case, you need to take action to remove your IP from the blacklist and prevent further malicious activity on that IP.
SORBS: This one lets you check your IP, netblock, or hostname. Type them in the search box, enter the CAPTCHA code, click on Check entry and see if you are safe or need to take action.
Barracuda: You can use the Check Reputation function to see if your IP address has been flagged as poor or suspicious in the reputation system.
DNSBL: That’s short for Domain Name System Blacklists. It’s a huge database that checks your IP against hundreds of blacklists. The result will show multiple blacklists where your IP might or might not have been flagged.
IP abuse reporting forms
IP address abuse reporting forms are an important tool for reporting incidents of IP address abuse to the relevant authorities. The process of using these forms may vary depending on the specific organization or platform, but generally speaking, you need to identify the type of IP abuse (spamming, phishing, etc.), and use the right form type for your situation.
Different organizations provide their own IP abuse reporting forms, but there are also third-party services you can use to report your problem. Let’s see a couple of examples of IP reporting organizations and services.
SpamCop: This is a popular service that allows you to report spam emails and other types of unwanted online messages.
Anti-Phishing Working Group: This organization provides a reporting form for reporting phishing scams and other types of online fraud.
Internet Crime Complaint Center (IC3): This is a partnership between the Federal Bureau of Investigation (FBI) and the National White Collar Crime Center (NW3C) that provides a reporting form for a wide range of online threats.
Google Safe Browsing: This service allows you to report unsafe websites and phishing scams to Google.
AbuseIPDB: This is a community-driven platform that allows you to report and search for IP address abuse incidents.
Understand how dangerous IP abuse can be
IP addresses are a valuable asset that must be guarded against cyber attacks. Unfortunately, we’ve seen many cases of security breaches and attacks that wrought havoc across networks and services.
One famous such case is the 2016 Mirai botnet attack. Mirai is malware that infects specific smart devices. When the devices are successfully infected, they turn into a network of remotely controlled bots called a botnet.
This newly created agent of chaos is often used to launch DDoS (Distributed Denial of Service) attacks.
Around 600,000 devices were infected, which were then used to generate a massive amount of traffic directed at Dyn (a former internet performance management and web application security company) and its servers. The attack caused widespread disruption to important websites, including Twitter, Netflix, and Amazon, as well as other services that relied on Dyn’s infrastructure.
The Mirai botnet attack is an important example of IP abuse, as it was able to exploit the vulnerabilities of IoT devices to create a massive DDoS attack that harmed major online services.
The attack demonstrated the need to secure Internet-connected devices and the need for stronger cybersecurity measures to prevent future IP abuses.
Understanding the importance of an IP database
An IP database is a collection of data that contains information about IP addresses. IP databases are used to store information about these IP addresses, such as their geographic location, internet service provider (ISP), and other related details.
IP databases are often used by businesses and organizations to help them identify and block malicious traffic, such as spam or hacking attempts, as well as to target specific geographical areas with their marketing campaigns. IP databases can also be used to track website visitors and analyze web traffic patterns.
There are various types of IP databases available, such as public databases and commercial databases. Public IP databases are typically freely available and contain basic information about IP addresses, such as their geographic location and ISP.
Commercial IP databases, on the other hand, typically provide more detailed and up-to-date information about IP addresses and are often used by companies for security and marketing purposes.
IP databases can be created and updated using various methods, such as by analyzing server logs, collecting data from web crawlers, or purchasing information from third-party providers. However, it is important to note that the accuracy of IP databases can vary, as IP addresses can be dynamic and can change over time, so it’s always a good idea to verify information with multiple sources.
Conclusion
In the world of the internet, your IP address is your virtual fingerprint, and when it falls into the wrong hands, it can be used for all sorts of malicious activities. From spamming to phishing to cyber attacks, the potential for IP abuse is vast and far-reaching.
With the rise of cyberattacks and other malicious activities, it is essential to learn about the various forms of IP abuse and how they can be detected. Phishing, malware, botnets, and open proxies are some common methods used by attackers to exploit IP addresses. Detecting IP abuse can be challenging, but there are tools such as network monitoring software that can be used to monitor network traffic for suspicious activity.