Do you know your IP address? Are you sure you are the only one who knows it?
Every day, malicious hackers use a technique called IP spoofing to mask their true identity and gain access to networks, computers, and even websites. A report from leading internet safety research company CAIDA found that there are nearly 30,000 unique spoofers attacking the network every day.
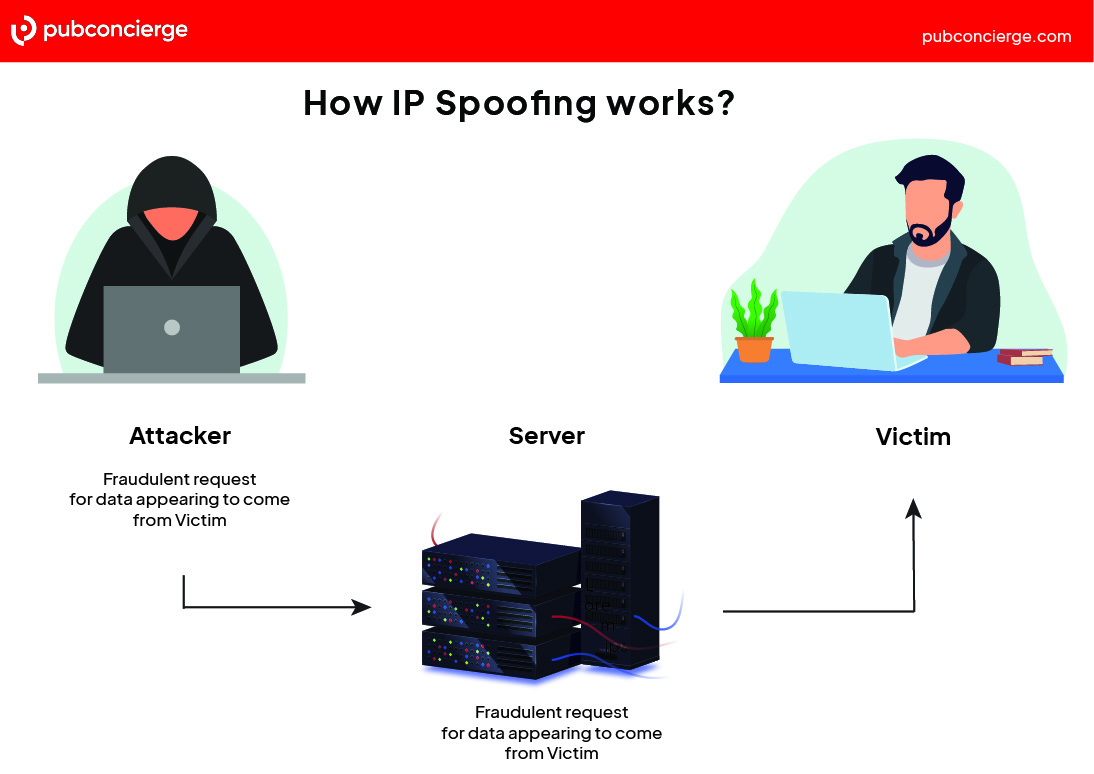
IP spoofing is a form of cyber-attack in which an attacker disguises their IP address to gain access to networks, computers, websites, and other online services. Once they get in, the attacker can access confidential information, steal data, or disrupt services.
IP spoofing is becoming an increasingly large problem – and has made the need for secure protocols and firewalls even more important.
So how does IP spoofing work? And how can you ensure that your network is fully protected from IP address spoofing attacks?
What Is IP Spoofing?
IP spoofing, in layman’s terms, is the act of masquerading as someone else on the internet. But instead of stealing your human identity to wreak havoc on your behalf, a hacker is actually stealing your IP address to access sensitive data or disrupt services.
To understand how this works, it’s essential to know an IP address: It’s a unique numerical identifier that each machine on the internet uses to identify itself and communicate with other computers. This IP address is assigned to your computer by your internet service provider (ISP).
When an attacker wants to spoof an IP address, they’ll use several techniques to probe the network, such as Address Resolution Protocol (ARP) cache poisoning, Domain Name System (DNS) hijacking, and others. Knowing a bit about how each works can help you set up the right security measures to protect yourself.
How Do Attackers Spoof IP Addresses?
There are a variety of methods attackers use to spoof IP addresses:
Source IP Spoofing
This is the most common method of IP spoofing. It involves modifying the packet headers in a network packet to make it appear as though it is coming from a different IP address.
This is most commonly used in Denial-of-Service (DoS) or Distributed Denial-of-Service (DDoS) attacks – malicious events that seek to overwhelm a target with packets of data.
Man-in-the-Middle (MitM) Attack
As the name suggests, a MitM attack intercepts communication between two systems. Hackers can spoof the IP address of one of the systems to make it seem like they are part of legitimate communication.
This allows them to intercept, send, and receive data intended for one of the original parties in the communication – including sensitive data such as usernames and passwords.
ARP Cache Poisoning
ARP is a protocol to map IP addresses to MAC (Media Access Control) addresses, which devices use to identify each other on the same network.
ARP cache poisoning is when an attacker sends falsified transmission packets or frames with incorrect information about the source or destination of a packet. This information is then stored in the ARP cache, which can be used to redirect traffic from one system to another.
DNS Server Spoofing
Like ARP cache poisoning, DNS server spoofing involves sending false data to a DNS server requesting the name of an IP address. This can redirect traffic from one system to another or block access to specific websites completely.
IP Address Spoofing in Email Headers
A particularly brazen type of IP spoofing involves forging the headers of an email to make it appear as though it was sent from an address other than the actual sender.
This attack is used to hide the identity of the real sender and can be used for malicious purposes such as phishing attacks or spreading malware.
Detecting IP Spoofing on Networks: How to Stop It
IP spoofing can be difficult to detect, but there are some steps that organizations and individuals can take to protect themselves:
1. Packet Inspection
One method by which organizations can detect IP spoofing is to inspect inbound and outbound network packets. This involves analyzing each packet’s source and destination addresses and other information, such as port numbers. If a packet appears suspicious, it can be investigated further.
2. Egress Filtering
Another method is to implement egress filtering on the network. This involves restricting outbound traffic from the network by only allowing packets with legitimate source IP addresses to leave the network. Think of it as a filter preventing spoofed traffic from the network.
3. Ingress Filtering
While egress filtering can prevent spoofed traffic from leaving the network, it won’t do anything to stop spoofed traffic from entering. To protect against this, organizations should use ingress filtering, which involves blocking inbound packets with source addresses that don’t belong to the organization.
4. Bogon Filtering
Bogon filtering is a technique used to filter out packets with source IP addresses not assigned by an internet registry. By blocking these packets, which are typically fake or spoofed, organizations can help protect their networks from malicious activity.
5. TTL Analysis
Every IP packet has a Time to Live (TTL) field in its header, which is decreased at each router it passes. If you capture a packet on your network and the TTL is too high or too low compared to what it should be, that could indicate a spoofed packet.
6. TCP/IP Stack Fingerprinting
Every system has specific ways to implement the TCP/IP stack. By observing these specific characteristics, it might be possible to identify spoofed packets. Network security tools like Nmap and Xprobe2 use this technique to determine the operating system of a remote host, which can help detect if an IP address is being spoofed.
7. IP Traceback
IP traceback is a technique used to trace the source of an attack. It works by injecting “traceback” packets into the network, which allows administrators to track the origin of malicious traffic, and thus identify spoofed IP addresses. Once the source is discovered, it can be blocked or monitored.
Steps You Can Take to Prevent IP Spoofing
The above detection steps can help you catch any spoofed IP addresses that may be targeting your network, but the best way to protect against these types of attacks is to prevent them from happening in the first place.
Fortunately, an ounce of prevention goes a long way when blocking and preventing IP spoofing attacks. Some of the steps you can take to prevent IP spoofing include:
1. Secure Your Router Configurations
Ensure that your router configurations, such as RIP and BGP, are secure and up-to-date. One of the top reasons that attackers are able to spoof IP addresses is because of weak or outdated router configurations.
2. Use Secure Protocols
Encrypting your data by using secure protocols like IPSec and TLS can help protect against IP spoofing attacks, as it will make it difficult for attackers to intercept and modify your traffic.
3. Utilize a VPN
Utilizing a Virtual Private Network (VPN) is another excellent way to secure your data from being intercepted and spoofed. VPNs encrypt all the data that travels through them, making it very difficult for attackers to bypass or modify it.
4. Install a Firewall
If a VPN is a bit much for your network, you can still protect against IP spoofing attacks by installing a firewall. Firewalls monitor incoming and outgoing traffic on a network and can stop any suspicious activity.
5. Audit Your System Regularly
Regularly analyzing your system for any suspicious activity, such as IP address spoofing attempts, is beneficial. This will help you identify and protect your network’s security gaps against potential threats.
6. Educate On The Risks
Whether you are looking to protect a home computer network or a large corporation, you can help protect against IP spoofing by educating users on its risks and the best practices they should follow.
Keep in mind that attackers are constantly developing new attack methods, so staying aware of security news and updates is the best way to ensure your network remains secure. By taking these steps, you can prevent IP spoofing and protect your data from falling into the wrong hands.
The Bottom Line
In the digital age, your IP address should have just as much protection as your physical address. When malicious actors can access your IP address, they can gain access to your sensitive data and cause all kinds of havoc.
Knowing what IP spoofing is and taking the proper steps to protect against it are crucial in making sure your network is secure from any malicious attacks. With a little knowledge and preparation, you can successfully stop a spoofed IP address before it does any lasting damage to your system.
As always, it’s essential to stay updated on the latest security news and best practices so that you can protect yourself against any new threats out there.